Cyber threats are no longer limited to a single device or entry point. Modern attacks move across endpoints, networks, cloud systems, and applications. Traditional security tools often struggle to keep up because they operate in isolation. This is where advanced solutions like EDR (Endpoint Detection and Response) and XDR (Extended Detection and Response) come into […]
Endpoint Security: What It Is, How It Works, and Why It Matters in Cybersecurity
Every device connected to a network laptops, smartphones, servers, tablets — represents a potential entry point for attackers. These devices, known as endpoints, are often the weakest link in cybersecurity. A single compromised device can give attackers access to an entire network. This is why endpoint security has become one of the most critical areas […]
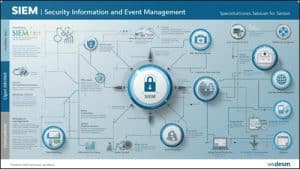
SIEM Explained: What It Is, How It Works, and Why It’s Critical for Cybersecurity
Cybersecurity is not just about preventing attacks — it’s about detecting them early, understanding them clearly, and responding quickly. The challenge is that modern networks generate massive amounts of data. Logs from servers, applications, firewalls, and user activity all create noise. Hidden within that noise could be a real attack. This is where SIEM becomes […]
Network Monitoring: What It Is, How It Works, and Why It Matters for Security
Most cyber threats don’t appear suddenly. They leave signals — unusual traffic spikes, unknown connections, slow performance, or strange data patterns. The problem is, without visibility, these warning signs go unnoticed. This is where network monitoring becomes critical. It allows you to track, analyze, and understand everything happening across your network in real time. Instead […]
DDoS Attack Explained: What It Is, How It Works, and How to Stop It
Websites don’t always go down because of technical failure. Sometimes, they are forced offline. One of the most common reasons behind sudden outages is a DDoS attack a type of cyberattack designed to overwhelm systems and make them unavailable to users. Unlike traditional hacking, attackers don’t need to break into your system. Instead, they flood […]
- 1
- 2
- 3
- …
- 296
- Next Page »